News Story
First Run of Cybersecurity MOOCs Taught by MC2 Faculty Finishes with a Flourish
The University of Maryland recently wrapped up the first offering of an online specialization in cybersecurity with a competition-style game that allowed students to put their cyber skills to the test against each other.
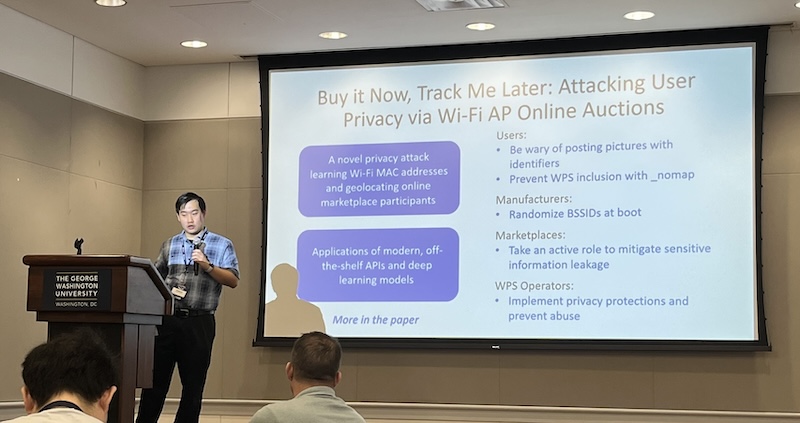
The specialization in cybersecurity—taught by faculty in the Maryland Cybersecurity Center (MC2) and launched in fall of 2014—was offered as a sequence of Massive Open Online Courses (MOOCs) on the popular Coursera platform.
Students could complete the specialization by taking a capstone course after having finished four courses offering a multidisciplinary perspective on current topics in cybersecurity: cryptography, software security, human-centered approaches for designing usable secure systems, and hardware security.
The courses were taken by more than 50,000 students from approximately 200 countries.
Ben Bederson, a professor of computer science with an appointment in the University of Maryland Institute for Advanced Computer Studies (UMIACS), tracked how many people participated in the courses—whether it was watching video lectures, submitting exercises, or browsing discussion forums.
“Since the courses are entirely voluntary, it is quite a bit different than a for-credit course,” he says. “I think of it more like buying a book for pleasure where some people skim, some read the first half, and some finish, but all receive value from the book.”
Michael Hicks, a professor of computer science with appointments in MC2 and UMIACS, led the capstone segment of the sequence.
The final project in the capstone course was centered on an online competition, where teams of students were first tasked with designing and building secure software. Other students were given the opportunity to discover and exploit flaws in the programs submitted by the first group, with a concluding segment devoted to developing patches for the vulnerabilities that were exposed.
The 69 teams—136 people—were scored separately in the rounds where they built software (“build it”) and hacked into others’ software (“break it”).
For the build it side, teams that managed to get working software earned a baseline score, and then earned more points for resisting attacks by other teams. For the break it side, teams that found at least one defect in another team's software earned a baseline score, and then got more points for additional defects they found, with more points for more serious defects.
Hicks believes the contest is a good way to gauge what students learned.
“Nowhere else can you write a non-trivial application and then have dozens of other teams turn it upside down to find problems with it,” he says.
“Nowhere else can you write a non-trivial application and then have dozens of other teams turn it upside down to find problems with it."
Michael Hicks
The four-person “Team JavaTheHut” came in first place in the first portion of the competition, while the two-person “Team Dark_Horse” took first place in the second category.
Helder Rodrigues, a member of “Team JavaTheHut” who lives in London, England, says he took the course to enhance his career in information security.
“I enjoyed all the courses and learned something from each one,” Rodrigues says. “For example, the software security course allowed me to better understand how to use secure development practices during the software development life-cycle, including the best approaches to test your software for vulnerabilities.”
He says the concluding competition was fun, but noted that each member of the team had to find time to collaborate while also working full-time.
“It reminded me of university where everyone brings hundreds of different ideas to the table and then you try to be democratic,” Rodrigues says. “When we started the system-building stage it was quite hard to agree on a one application architecture, but once we agreed it was full-steam ahead.”
Juraj Kosik, a member of “Team Black_Horse” who lives in Slovakia, says he found the competition to be “nice, real-life, security training.”
As a security engineer, he says the specialization tied in well with his work.
“I found the hands-on tests to be especially useful,” Kosik says. “Some of the best topics included buffer overflow hacking and memory analysis, hardware security in general, the logic behind crypto-algorithms, and how to improve ergonomy of a security system.”
Hicks says the four courses in the cybersecurity specialization will now each be offered every semester, and the capstone competition will run again on Coursera in Fall 2015.
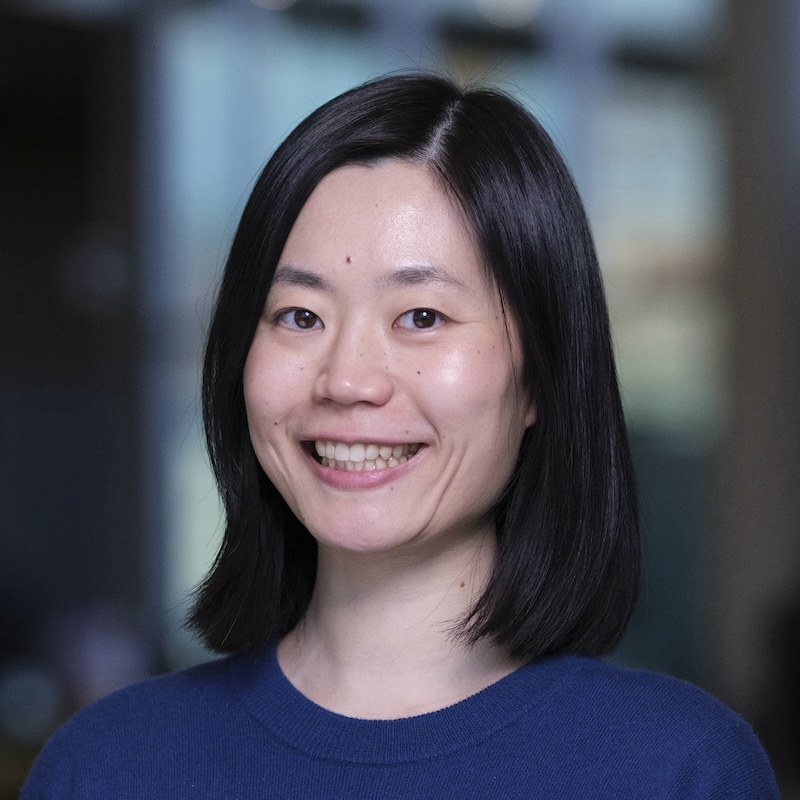
Other MC2 faculty members that taught the cybersecurity specialization MOOCs were Gang Qu (electrical and computer engineering), MC2 Director Jonathan Katz (computer science and UMIACS), and Jen Golbeck (College of Information Studies).
Learn more or sign up for the specialization in cybersecurity here.
—Story by Melissa Brachfeld